APT Profile – UNC1151
Fusing Technical and Social Vulnerabilities
- 25 May 2023
- Kerstin Zettl-Schabath; Jakob Bund; Lena Rottinger; Camille Borrett
- EN
About UNC1151
UNC1151 is a state-integrated hacking group (members of the Belarusian military, potentially supported by “quasi- seconded” officers of the Russian military intelligence service) and/or state-ordered hacking group (Belarusian military actors operating as proxies of Russian military intelligence). If, as reported by industry experts, UNC1151 operates from Belarusian soil and (at least for a part of its activities) coordinates with Russian military intelligence actors, as indicated by Recorded Future reporting from March 2022, the group’s further characterisation depends on whether its members are part of Belarusian military units or Russian citizens/military intelligence officers operating from Belarus. Based on the reported close connection between Belarusian and Russian intelligence services, Belarusian responsibility for the execution of UNC1151 activities, at the direction of or in consultation with Russian military intelligence actors, appears plausible.
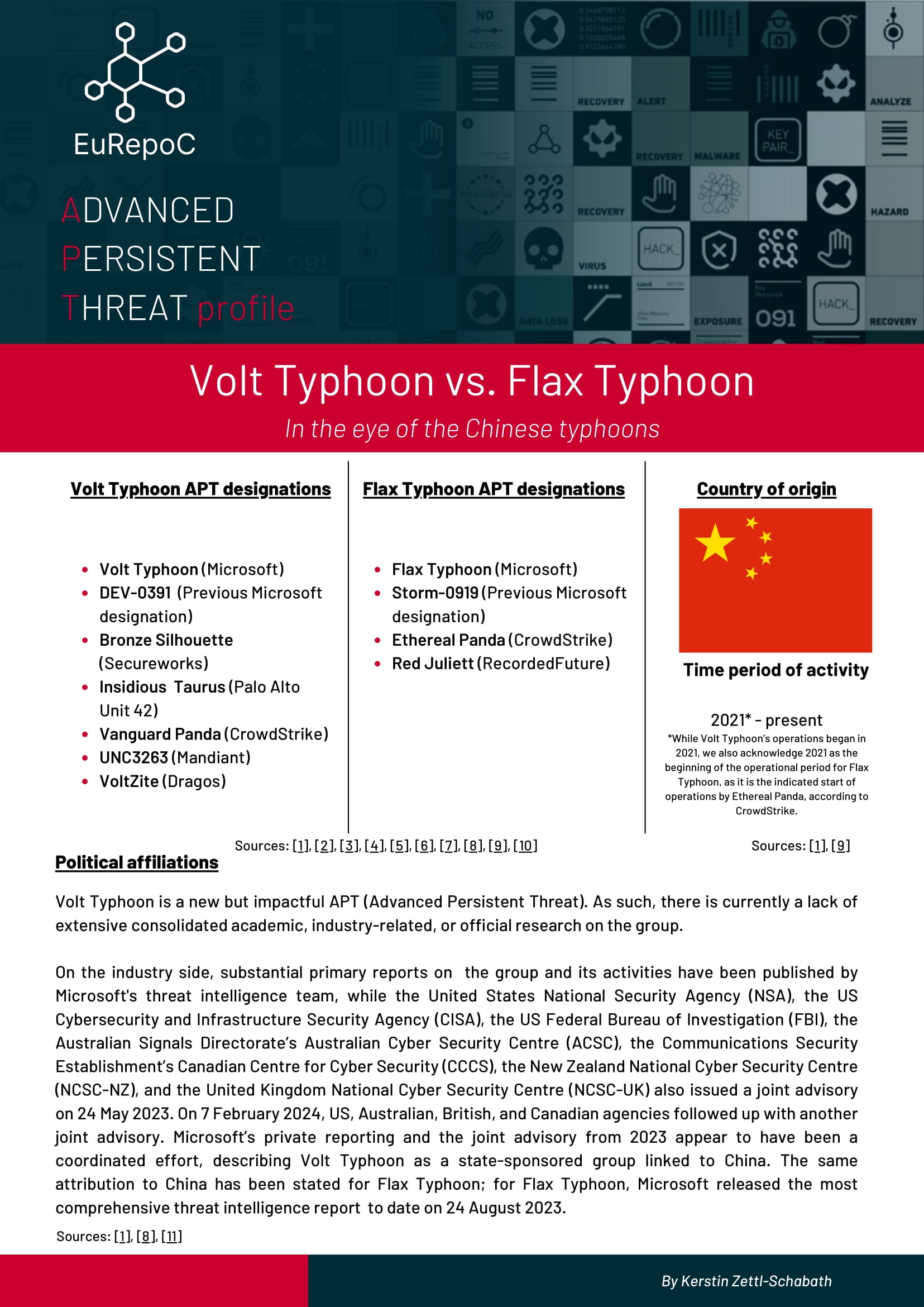
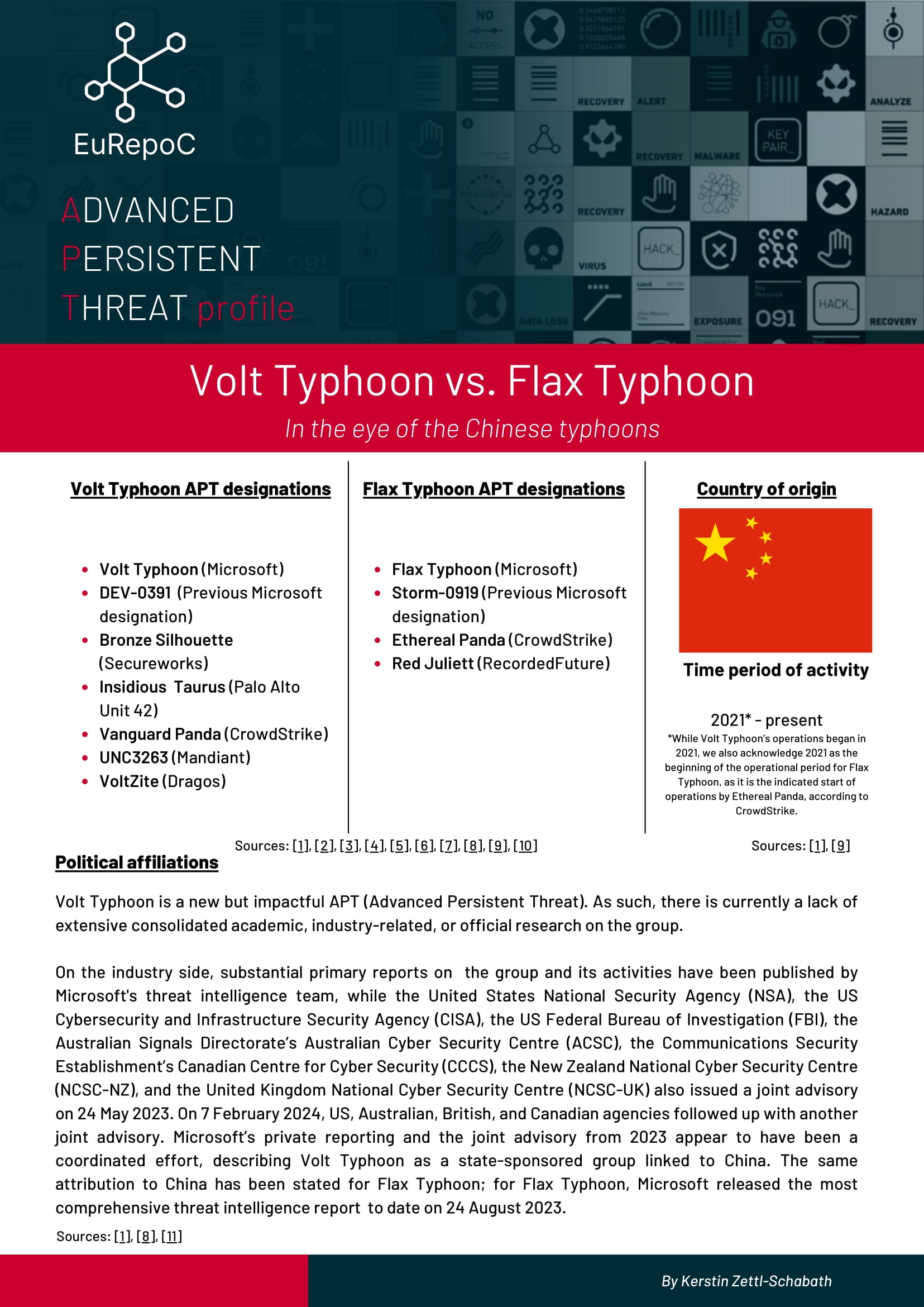
Associated APT designations
- UNC1151 (FireEye/Mandiant, ThreatConnect)
- TA445 (Proofpoint)
- PUSHCHA (Google TAG)
- Storm-0257/DEV-0257 (Microsoft)
- Moonscape (Secureworks)
- UAC-0051 (CERT-UA)
- Ghostwriter
Country of origin
Period of activity
Since at least 2017-today
More APT profiles
- Research and Analysis