APT Profile – APT3/Boyusec
Going for industrial secrets, going dark...?
- 26 September 2023
- Zettl-Schabath, Kerstin; Butz, Benjamin; Borrett, Camille
- EN
About APT3/Boyusec
APT3 mainly focused on targets of strategic importance for the Chinese Communist Party, as well as
targets vital for China’s economic interests and military modernisation. The attacked entities included
targets in aerospace, defence, construction and engineering, telecommunications, and transportation.
The group’s political affiliation was mainly revealed in 2017 when various actors published attribution
statements that linked APT3 with the Chinese information security company Guangzhou Boyu Information
Technology Company, Ltd. (Boyusec), based in Guangzhou, which was acting as a front for the Chinese
Ministry of State Security (MSS). In 2014, Boyusec had established a joint active defence laboratory (ADUL) in cooperation with Guangdong ITSEC, a subordinate to the China Information Technology Evaluation Center
(CNITSEC) organisation, which is run by the MSS. CNITSEC is said to execute vulnerability testing and
reliability assessments of software for the Ministry. The vulnerabilities found by CNITSEC were then
allegedly used for intelligence operations by the MSS.
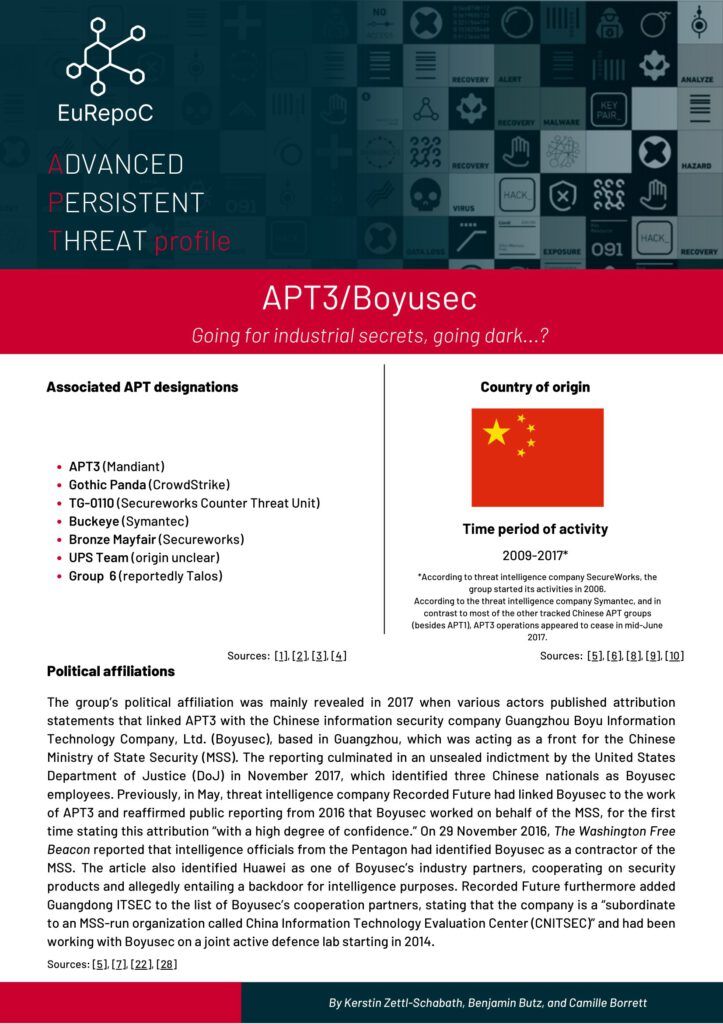
Associated APT designations
- APT3 (Mandiant)
- Gothic Panda (CrowdStrike)
- TG-0110 (SecureWorks Counter Threat Unit)
- Buckeye (Symantec)
- Bronze Mayfair (SecureWorks)
- UPS Team (origin unclear)
- Group 6 (reportedly Talos)
Country of origin
Period of activity
2009-2017*
*According to threat intelligence company SecureWorks, the group started its activities in 2006.
According to the threat intelligence company Symantec, and in contrast to most of the other tracked Chinese APT groups (besides APT1), APT3 operations appeared to cease in mid-June 2017.
More APT profiles
- Research and Analysis